Anti-DDoS
Are you interested in Anti-DDoS or do you have any questions regarding Anti-DDoS? I will be happy to answer your questions in a free consultation!
T-Systems International GmbH
Tino Fehnle
Anti-DDoS
Many publicly accessible corporate websites are subject to hacker attacks. A common scenario is when a website is overloaded by a flood of requests from different IP addresses within a short period of time. This is what is known as a distributed denial-of-service attack (DDoS). The sheer amount of requests brings the website to its knees, rendering the service unavailable. For owners, this is a highly unpleasant scenario.
Website hosts can protect themselves from these kind of attacks with a software-based security feature: Anti-DDoS automatically detects DDoS attacks by checking incoming requests for malicious intent. In the event of an attack, it redirects spurious requests and ensures that the service remains online without sapping any additonal resources.

The Anti-DDoS service protects elastic IP addresses (EIPs) against DDoS attacks at the network and application levels, immediately sending an alert when an attack is detected. In addition, Anti-DDoS optimizes bandwidth use and ensures a stable operation of users' services.
Anti-DDoS monitors service traffic from the web to the EIPs in order to detect attacks traffic in real time. It then purges the attack traffic according to previously defined defense policies by the user, so that services return to normal. The service also generates monitoring reports that provide users with a clear assessment of their network security.

Anti-DDoS is a free add-on component that complements the range of hardware security functions in Deutsche Telekom's data centers. The Open Telekom Cloud's comprehensive and platform-wide runtime monitoring ensures that DDoS attacks are automatically detected and defended against.

Using the Anti-DDoS service, users can define threshold values which can be used e.g. to specifically defend against challenge collapsar (CC) attacks. The Open Telekom Cloud provides reports with detailed information on the attacks, so that users have access to a comprehensive overview at any time.
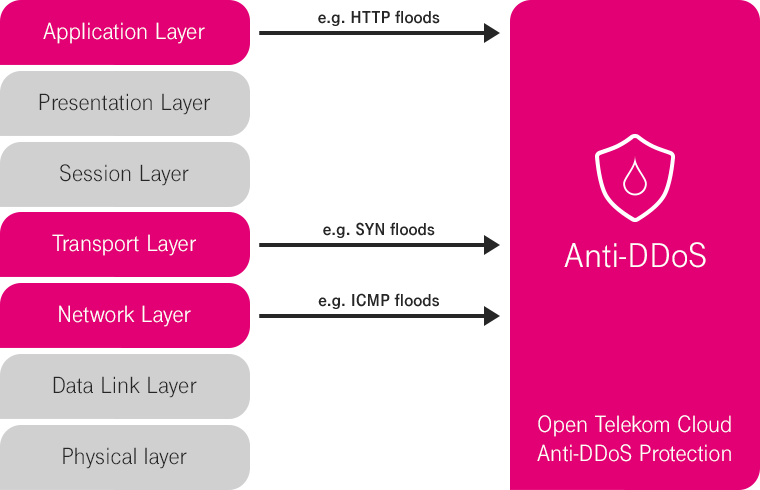
The Anti-DDoS service protects against attacks on the third (network), fourth (transport) and seventh (application) layer.
Third and fourth layer DDoS attacks are a type of volumetric DDoS attack and rely on extremely high volumes of data (floods) to slow down web server performance, consume bandwidth, and ultimately hinder access for legitimate users. Including attacks such as synchronized (SYN) floods, these are the most common attack vectors used to overload the capacity of application servers, but are able to be detected and redirected via signatures.
Seventh layer DDoS attacks aim to overload specific elements of an application server's infrastructure. These attacks are particularly complex, inconspicuous, and difficult to detect as they are similar in appearance to legitimate website traffic. With attacks like HTTP GET flood, attackers try to send a huge flood of requests to the server in order to overload its resources.

Server protection from attacks such as SYN floods, SYN-ACK floods, FIN floods, RST floods, UDP floods, ICMP floods, and state-exhaustion attacks.

Server protection from attacks such as HTTP GET/POST floods, CC attacks, or HTTP slow header/POST und HTTPS floods.
The included IP reputation service supports millions of IP addresses and monitors both inbound and outbound traffic. This allows requests from botnets to be quickly and easily detected and filtered. The Anti-DDoS service ensures that only unwanted traffic is filtered out for both UDP and TCP cleaning.
Websites are vulnerable to DDoS attacks, which can ultimately cause them to crash. However, Anti-DDoS can defend against multi-layer (4 through 7) attacks, helping to improve a customer's browsing experience. Additional use of the Web Application Firewall (WAF) can also avert attacks such as SQL Injection or Cross Site Scripting (XSS).
Advantages
Possible scenarios
Websites | Portals | E-Commerce
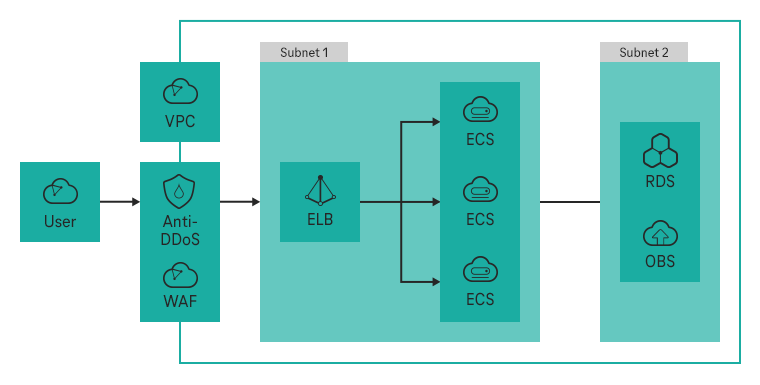
Anti-DDoS supports the elastic IP addresses used by elastic cloud servers, elastic load balancing instances, and bare metal servers in the Public Cloud.
Anti-DDoS protection is automatically enabled for the elastic IP addresses you purchased. If protection is not yet enabled for an IP address you own, you can activate it directly in the Anti-DDoS console. For a detailed guide, please follow the instructions in the Help Center.
Anti-DDoS helps users handle traffic attacks with ease. It can accurately detect connection exhaustion and attacks on slow connections and can help users defend against the following attacks:
A detailed overview of all functions can be found in the Help Center.


Are you interested in Anti-DDoS or do you have any questions regarding Anti-DDoS? I will be happy to answer your questions in a free consultation!
T-Systems International GmbH
Tino Fehnle
